The Flipper Zero, a Swiss Army knife of security tools, has taken the digital nomad world by storm. Its compact size and plethora of features, from emulating RFID cards to analyzing radio signals, make it a dream tool for security enthusiasts and hackers alike. But with great power comes great responsibility, and the question of Flipper Zero’s legality looms large.
Legality Lowdown:
The good news is, owning a Flipper Zero is generally legal in most countries, including the US. However, the devil is in the details:
- Usage Matters: Using a Flipper Zero for malicious purposes like card skimming, unauthorized hacking, or interfering with critical infrastructure is illegal almost everywhere. Remember, ethical hacking is key!
- Local Laws Vary: Specific regulations regarding Flipper Zero ownership and usage can differ greatly between countries. Always check your local laws before bringing yours on your digital nomad adventures.
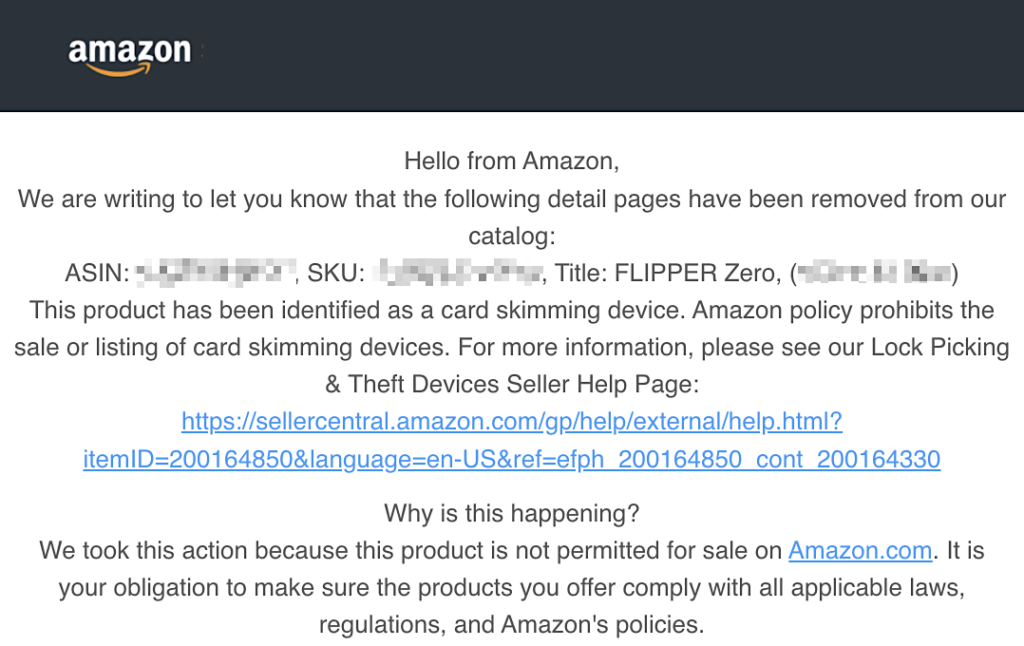
- Amazon Ban: Flipper Zero is currently not allowed on Amazon due to concerns about potential misuse.
Flipper Zero Alternatives:
If Flipper Zero raises legal concerns or isn’t readily available, fret not! Several alternatives cater to your security toolkit needs:
- HackRF One: A powerful software-defined radio (SDR) for exploring radio frequencies, offering similar functionality to Flipper Zero but with a steeper learning curve.
- NFC Tools Pro: An Android app that reads and writes NFC tags, a more limited but user-friendly option for basic RFID exploration.
- ESP32: A versatile development board that can be programmed for various security tasks, requiring some coding skills but offering immense customization potential.
ESP32 Resources for Security Tasks Official Sources:
Espressif Systems – ESP-IDF (Espressif Integrated Development Framework)
Community and Forums: ESP32 Forum.
Beyond the Big Names:
For budget-conscious nomads or those seeking unique options, consider these gems:
- RTL-SDR: A cheap and popular USB SDR for radio experimentation, offering a great entry point into the world of RF hacking.
- Yard Stick One: A multi-tool pen with NFC reading/writing capabilities, perfect for covert security checks on the go.
- Proxmark 3: A powerful RFID reader/writer for advanced users, offering an in-depth exploration of RFID protocols.
Import Hacks and DIY Delights:
Customs issues can be a buzzkill, but fear not! Here are some tips for smoother imports:
- Declare it: Transparency is key. Honestly declaring your Flipper Zero at customs can go a long way.
- Know your limits: Check import restrictions for your destination country. Exceeding quantity limits might raise eyebrows.
- DIY Delight: Building your own SDR or RFID tool can be a rewarding and legal alternative, offering deep customization and a unique learning experience.
Similar Devices and App-tastic Alternatives:
Looking for app-based options or devices with similar functionality? Check out these cool options:
- NFC Reader: A plethora of mobile apps can read and write NFC tags, offering basic functionality on the go.
- Wireshark: This popular network protocol analyzer runs on various platforms, providing deep insights into network traffic, perfect for security-conscious nomads.
- Kali Linux NetHunter: This Android-based penetration testing platform turns your phone into a powerful security toolkit, offering ethical hacking capabilities on the move.
Remember: Regardless of your chosen tool, responsible and ethical use is paramount. Remember, the digital nomad lifestyle is about exploration and learning, not illegal activities. So, use your security toolkit wisely and make the most of your digital nomad adventures!
Bonus Tip: Many online communities and forums cater to Flipper Zero and similar tools. These communities offer valuable resources, tutorials, and support, helping you get the most out of your chosen hardware. Dive in, connect with fellow nomads, and hack your way to a more secure and informed digital nomad experience!
I hope this information empowers you to make informed choices about Flipper Zero and its alternatives. Remember, knowledge is power, and responsible use is the key to unlocking the full potential of these fascinating security tools. Now, go forth, explore, and hack ethically!




[…] It is important to note that the legality of Flipper Zero and other hacking tools is a complex issue that varies by jurisdiction. For more information on the legality of Flipper Zero, check out the article “Is Flipper Zero Legal? Understanding The Legality Of This Powerful Security Tool.” […]